Digital Notary Security: The Future of Remote Online Notarizations
What is Digital Notary Security?
Key Features of Digital Notary Security
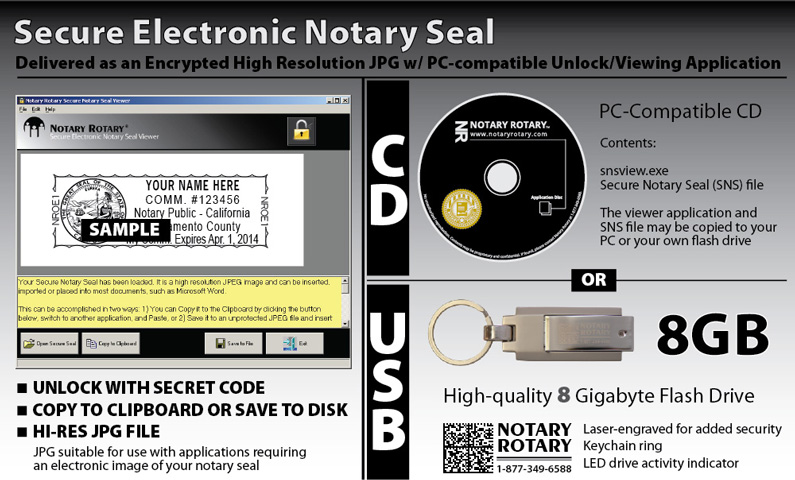
- Advanced Encryption Techniques: Digital Notary Security employs state-of-the-art encryption methods to safeguard electronic documents, minimizing the risk of fraud and unauthorized access.
- Blockchain Technology: The integration of blockchain technology provides an immutable and tamper-proof record of notarized documents, ensuring the authenticity and integrity of the transaction.
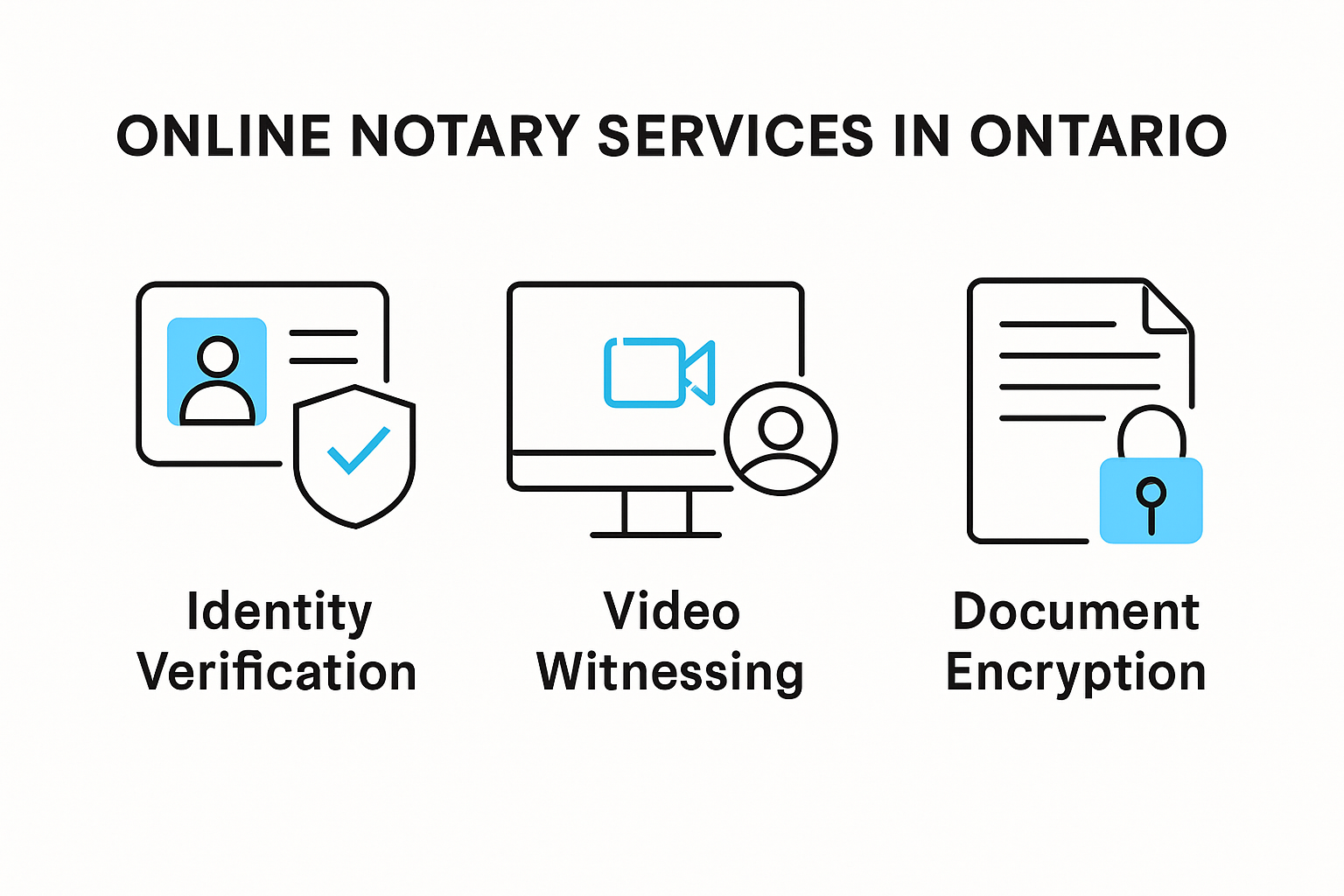
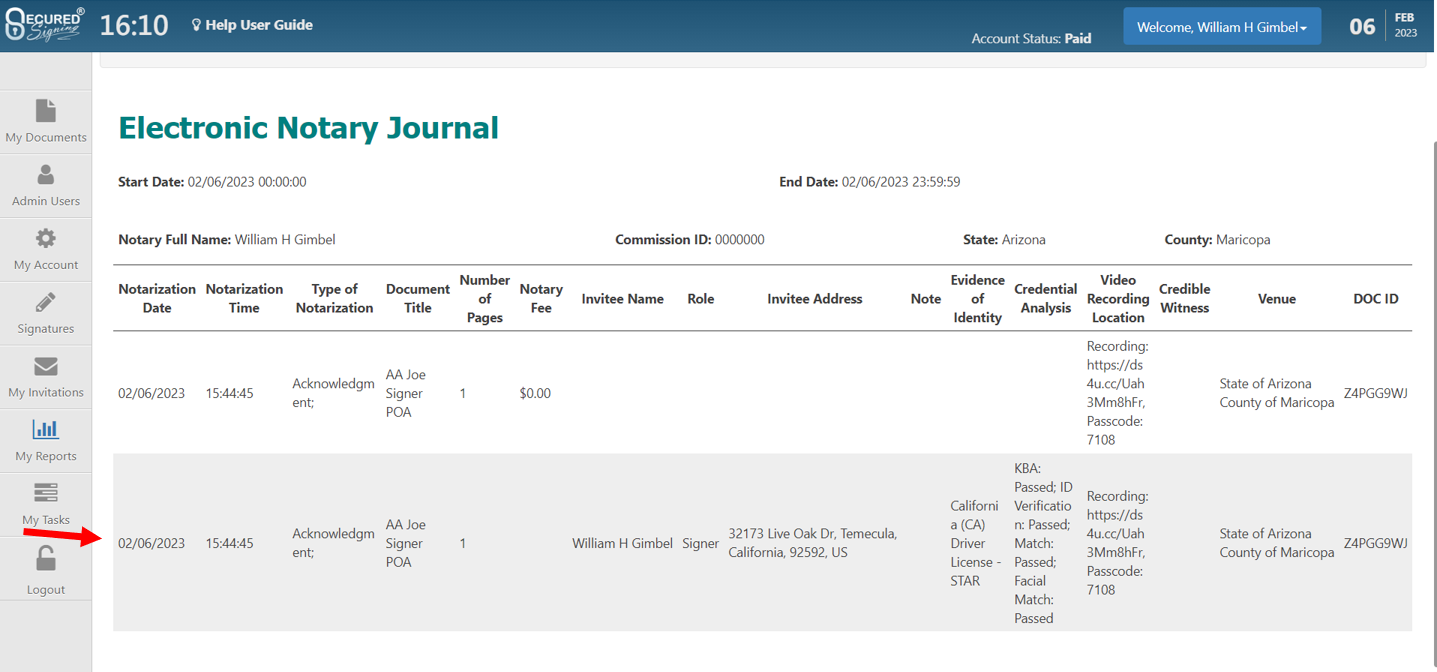
- Identity Verification: RON platforms employ AI-driven verification methods to authenticate the identity of signers, reducing the risk of identity theft and impersonation.
- Decentralized Platforms: Integration with decentralized platforms promotes broad accessibility, enabling secure and efficient notarization from anywhere in the world.
Benefits of Digital Notary Security
- Enhanced Security: Advanced encryption techniques and blockchain technology ensure the security and integrity of electronic documents.
- Cost Savings: Digital notary services eliminate the need for paper-based processes, saving costs associated with printing, storage, and transportation of documents.
- Streamlined Identity Authentication: AI-driven verification methods reduce the risk of identity theft and impersonation, streamlining the identity authentication process.
- Broader Accessibility: Integration with decentralized platforms promotes broad accessibility, enabling secure and efficient notarization from anywhere in the world.
Best Practices for Digital Notary Security
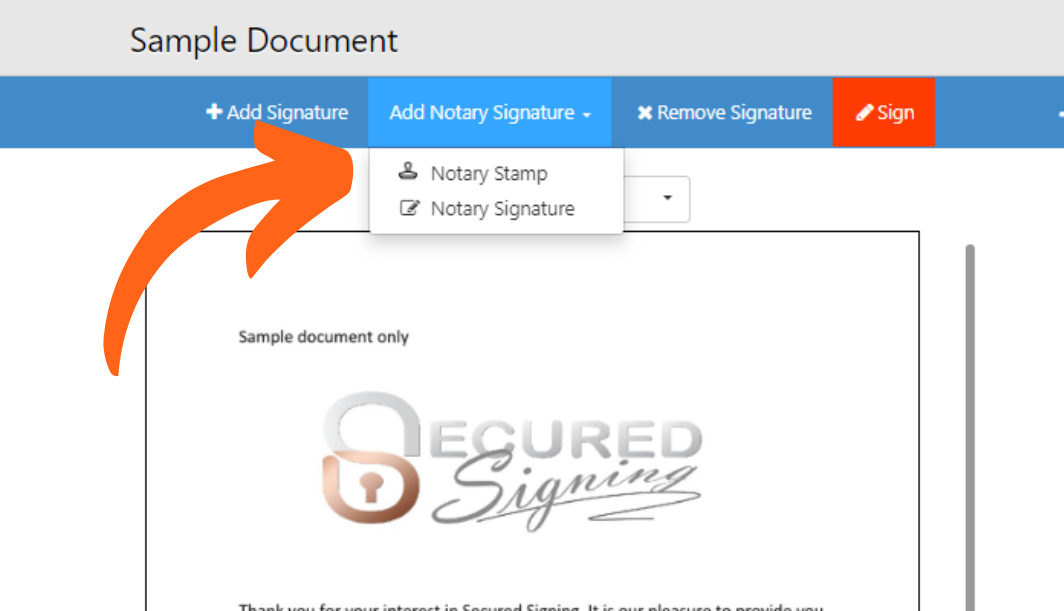
- Choose a Reliable Platform: Select a reputable RON platform that employs advanced security measures, including encryption and identity verification.
- Use a Digital Certificate: Obtain a digital certificate from a trusted Certification Authority to verify notary public identity and ensure the security of notarized documents.
- Implement Regular Updates: Regularly update your software and systems to ensure you have the latest security patches and features.
- Conduct Security Audits: Perform regular security audits to identify vulnerabilities and ensure compliance with regulatory requirements.
Conclusion