G Network Security Setup for IT Infrastructure
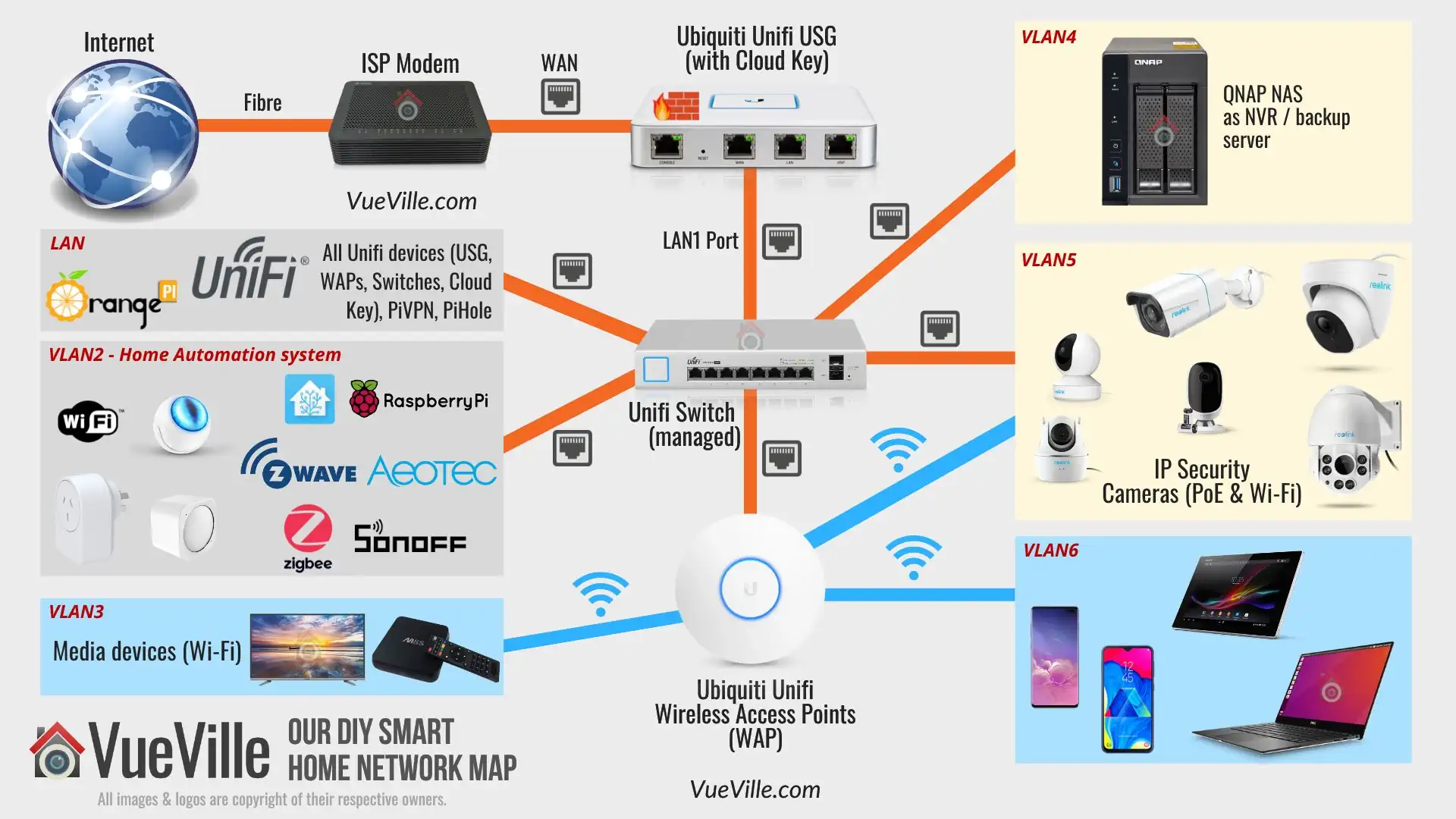
The foundation of security, availability, and performance for any IT infrastructure is proper network configuration. Network segmentation is a critical aspect of this, significantly reducing the ability for an adversary to reach and exploit other systems. In this article, we will explore a G network security setup for IT infrastructure, highlighting the importance of network security and providing a step-by-step guide to implementing a robust security measure.
Understanding Network Security Infrastructure
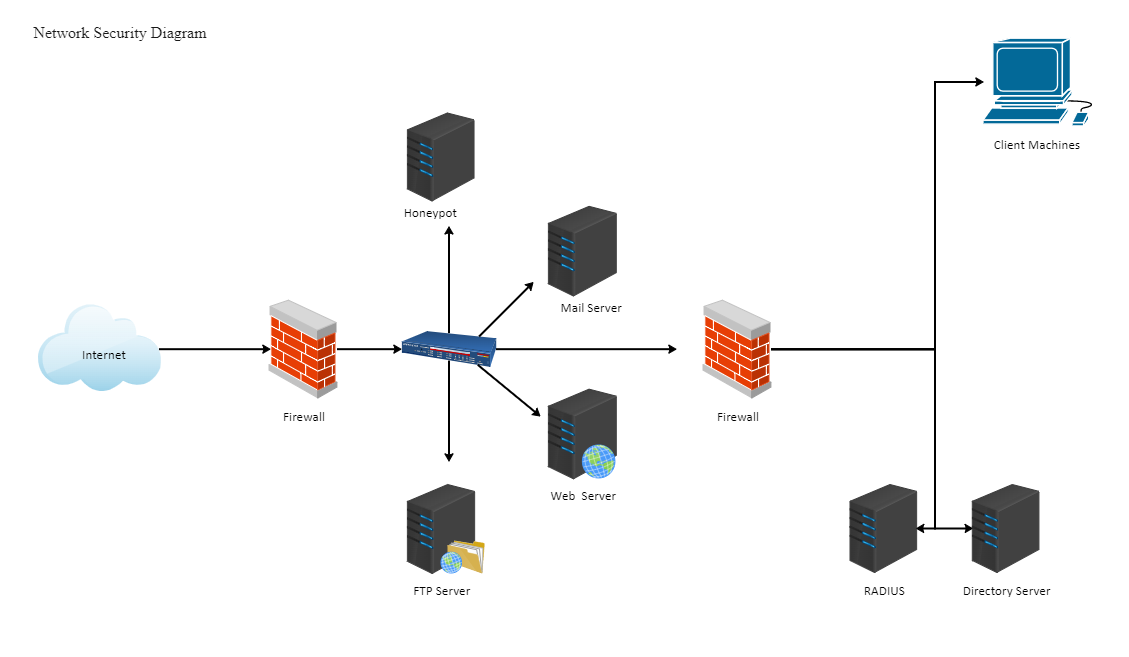
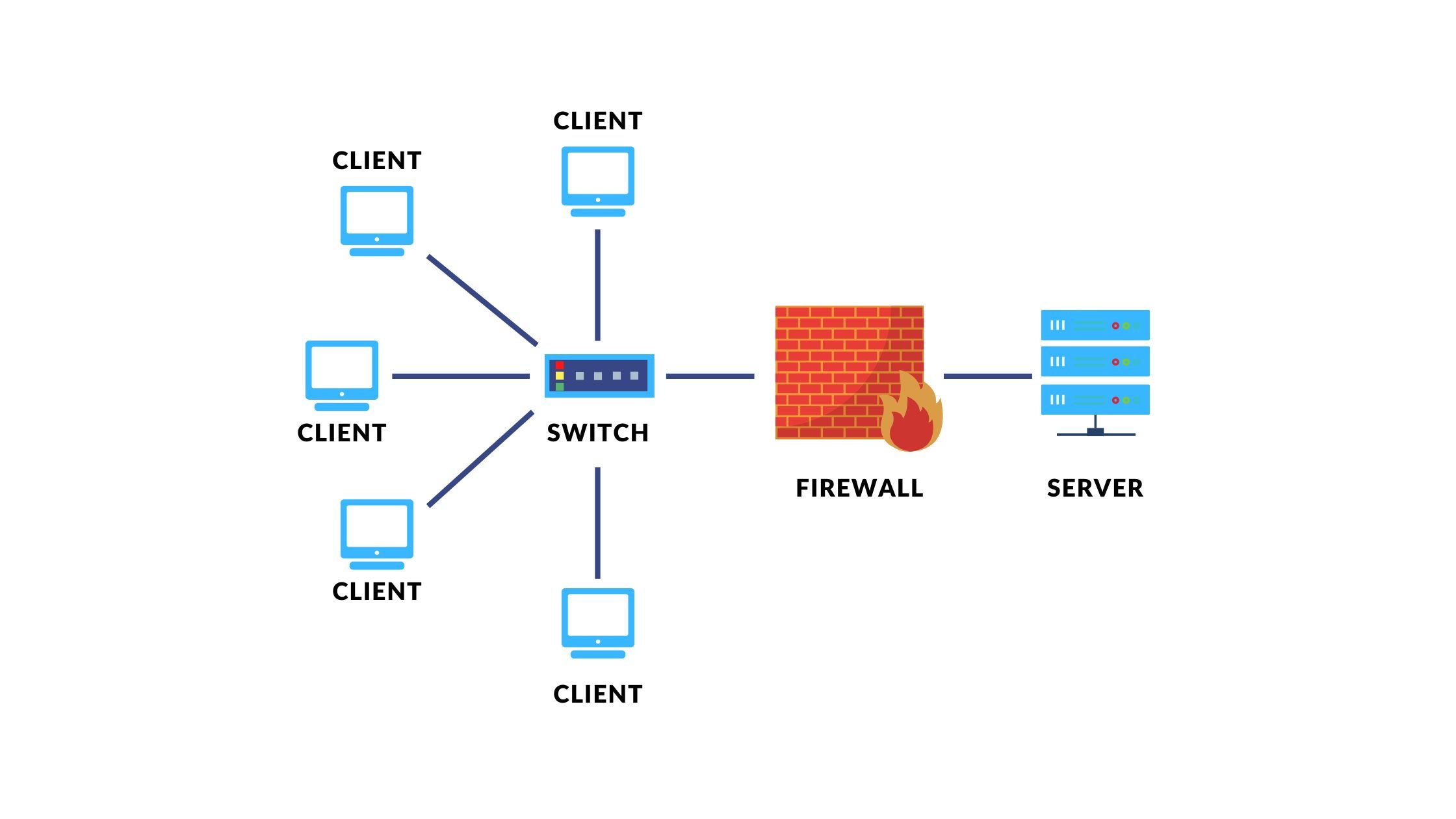
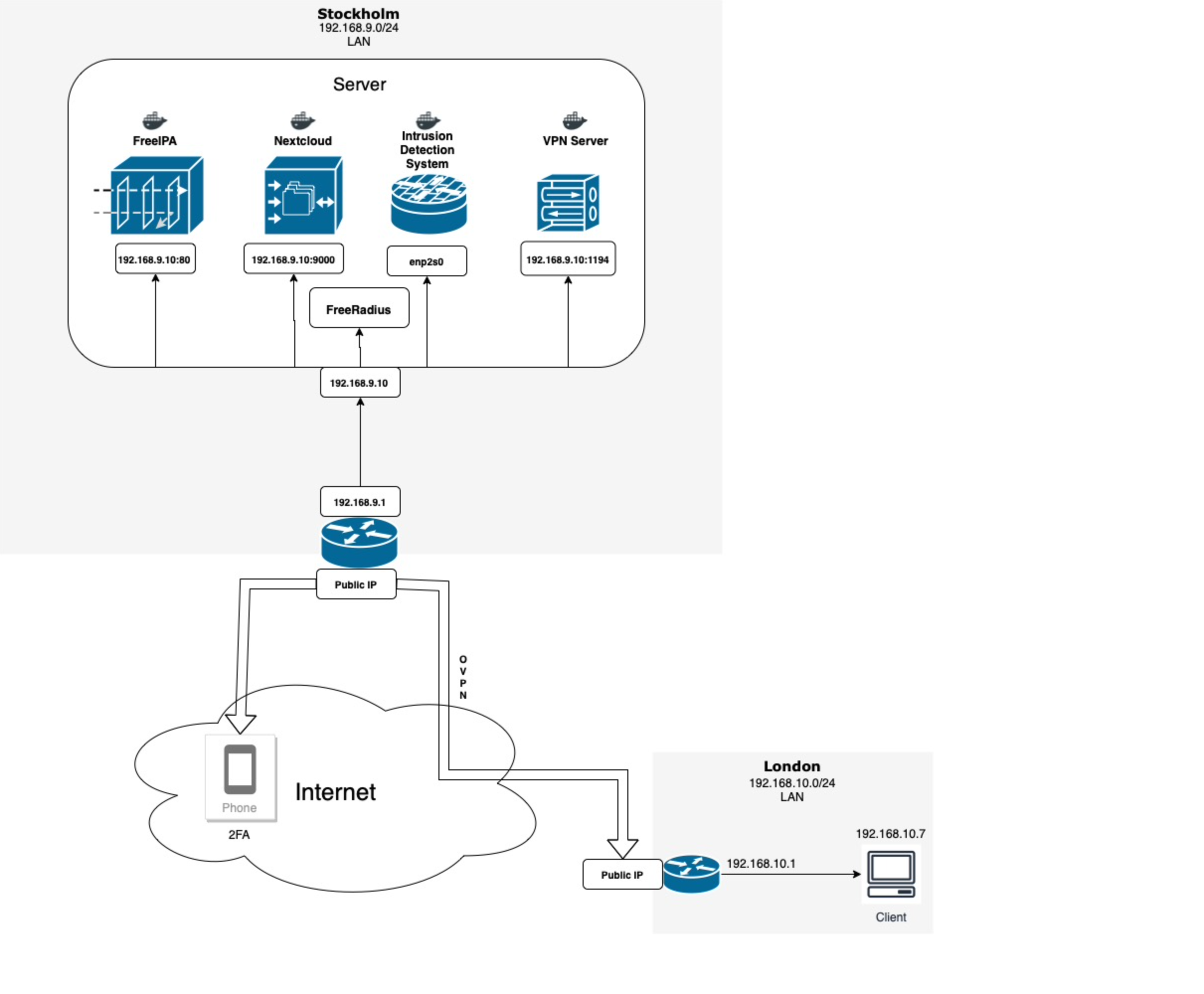
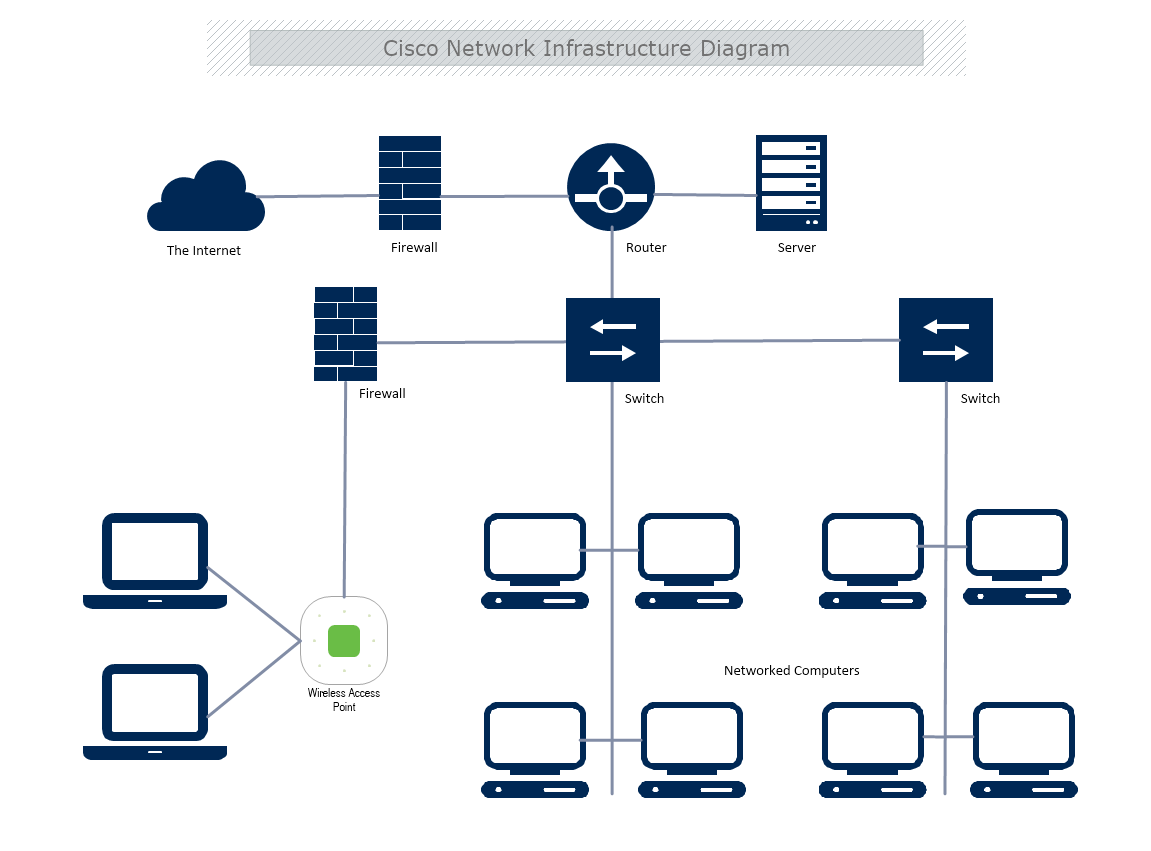
Network security infrastructure is vital for protecting data. It encompasses various components, including firewalls, intrusion detection and prevention systems, virtual private networks (VPNs), and access control systems. A well-designed network security architecture provides an organization with visibility and control over its entire network infrastructure and offers the tools needed to defend it against various cyber threats.
Key Components of Network Security Infrastructure
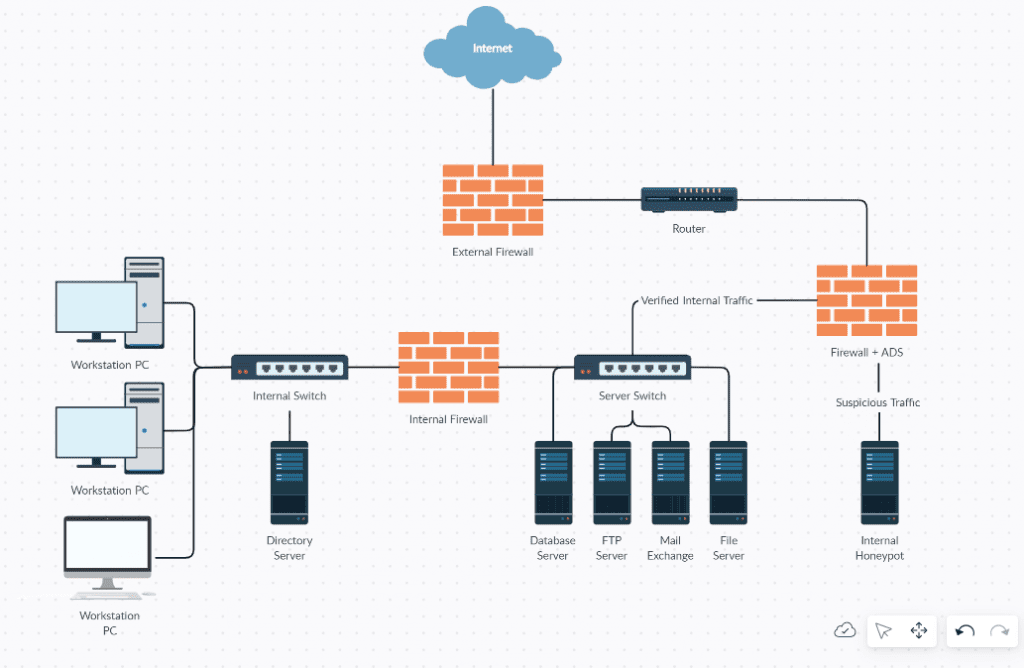
- Firewalls: Prevent unauthorized access to network resources
- Intrusion Detection and Prevention Systems: Detect and prevent malicious activity on the network
- Virtual Private Networks (VPNs): Encrypt network traffic and provide secure access to network resources
- Access Control Systems: Manage who has access to network resources and what they can do with them
Implementing G Network Security Setup for IT Infrastructure
Implementing a G network security setup for IT infrastructure involves several critical steps. These include: