Setting Up a G Router for Secure Data Transfer: A Step-by-Step Guide
With the increasing reliance on wireless networks for internet access, it's imperative to set up a G router for secure data transfer to safeguard your sensitive information. In this article, we'll walk you through the process of setting up your G router to ensure a secure and stable connection.
Understanding the Basics of A G Router
- A G router, also known as a wireless router or a Wi-Fi router, is a device that connects your home network to the internet via Wi-Fi or a physical Ethernet cable.
- It's essential to have a good G router to ensure a fast and secure connection for all your devices, including computers, laptops, smartphones, and smart TVs.
- When setting up a G router, it's crucial to configure the router's settings to establish a secure connection for data transfer.

Setting Up Your G Router for Secure Data Transfer
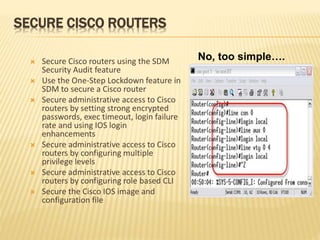
- Change the Default Admin Password: The first step in setting up your G router for secure data transfer is to change the default admin password. This will prevent unauthorized access to your router's settings.
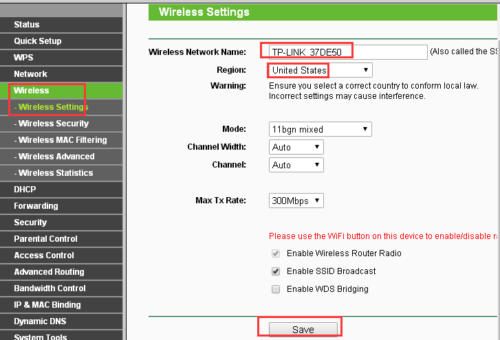
- Configure Wireless Settings: Configure your router's wireless settings to ensure a secure connection for data transfer.
- Set Up Quality of Service (QoS): Configure QoS settings to prioritize critical applications and ensure reliable data transfer.
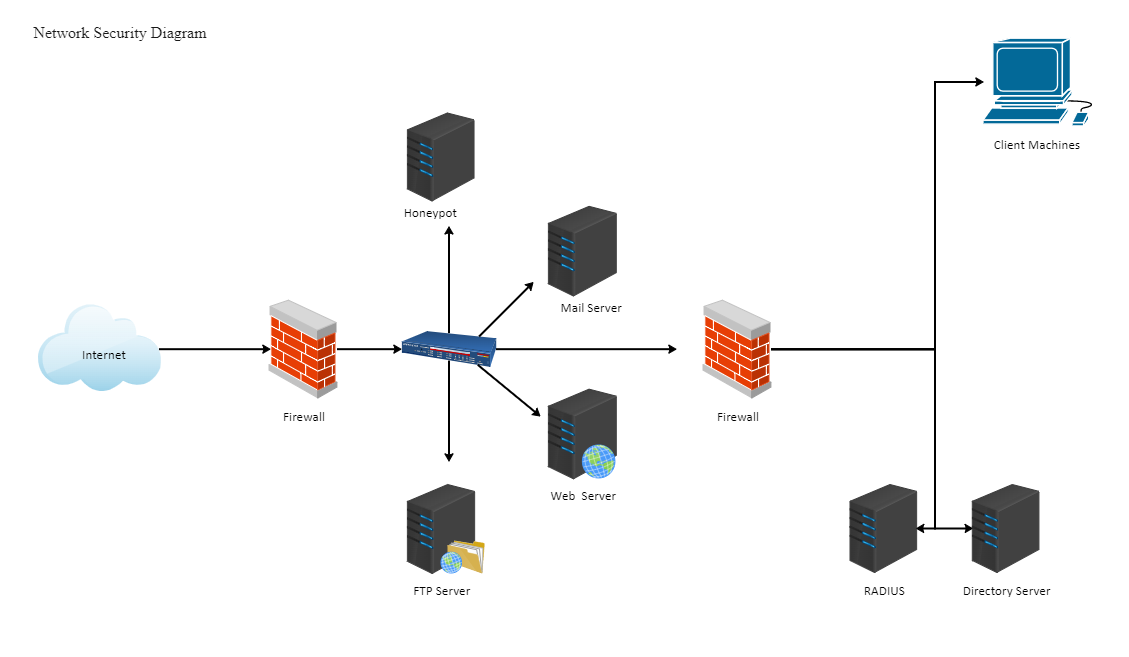
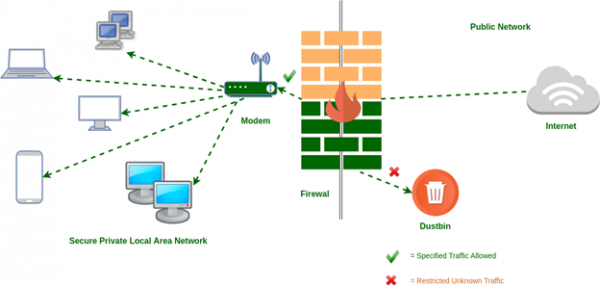
- Enable Firewall Settings: Configure your router's firewall settings to block unauthorized access to your network.
- Update Firmware: Regularly update your router's firmware to ensure you have the latest security patches and features.
- Set Up Network Address Translation (NAT): Configure NAT settings to ensure a secure connection for data transfer.
Locate the default admin password on your router's documentation or online manual. Log in to your router using the default admin username and password. Go to the administration section and change the admin password to a strong, unique password.
Change the Wi-Fi network name (SSID) and password to something more secure. Enable WPA2 encryption and set up a guest network to isolate visitors from your main network.
Set up QoS rules to prioritize applications such as video streaming, online gaming, and VoIP calls. This will ensure that critical applications have a consistent and stable connection.
Enable the built-in firewall and configure custom rules to block incoming traffic from unknown sources. This will prevent hackers and malware from gaining access to your network.
Check your router's manufacturer website for firmware updates. Follow the instructions to update the firmware and ensure your router is running the latest version.
Set up NAT filtering to block incoming traffic from unknown sources. This will prevent hackers and malware from gaining access to your network.
















.png)